[Phoenix, AZ] – [July 2025] – SanTrac Technologies is proud to have attended and supported SRP’s 30th Anniversary Supplier Diversity Celebration, held on Tuesday, June 3, 2025, at the PERA Pavilion in Tempe, Arizona. The event commemorated three decades of SRP’s commitment to uplifting small, local, and diverse businesses — a mission that aligns closely with SanTrac’s own values.
SanTrac Technologies Joins Salt River Project (SRP) in Celebrating 30 Years of Supplier Diversity and Economic Empowerment
Business Interrupted: The Unexpected Disaster Your IT Provider Should Be Planning For
Your Phone Can Be Tracked – And It’s Easier Than You Think

Most of us carry our phones everywhere, trusting them with everything from passwords to private business conversations. But here’s the unsettling truth: phone tracking is far more common – and easier – than most people realize.
Whether it’s a jealous partner, a disgruntled employee or a cybercriminal targeting your business, anyone with the right tools can monitor your location, read your messages or even access sensitive business data without you ever knowing.
The Compliance Blind Spot: What You’re Missing Could Cost You Thousands
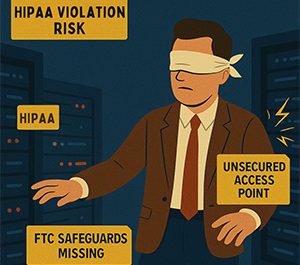
Many small business owners operate under the misconception that regulatory compliance is a concern solely for large corporations. However, in 2025, this belief couldn’t be further from the truth. With tightening regulations across various sectors, small businesses are increasingly in the crosshairs of compliance enforcement agencies.
The Hidden Cost Of “Cheap” IT
Are You Posting Too Much Information to Social Media?
When the Dark Web Has Your PII
How a Supply Chain Attack Triggered a Lawsuit
Introduction
A lawsuit is arising against a software provider for a data breach that impacted 500K people last year.
The Memphis-Shelby County Schools (MSCS) filed a lawsuit against PowerSchool, their California-based software company, due to a significant data breach that occurred in December 2024. This breach compromised private data belonging to about 500K current and former students, and over 23K employees.
Stuck On Updating? How To Fix Common Windows Update Failures

Nothing tests your patience quite like the “Checking for updates…” screen on a Windows PC — unless it ends with a failed update message, just to add insult to injury. Windows Update issues are a common headache for many users, interrupting workflow and potentially leaving systems vulnerable. This article offers practical solutions to get your Windows Update service running smoothly again.
How To Harness Threat Intelligence For Real Impact

As cyberthreats become more sophisticated, your business’s focus shouldn’t just be on collecting more data about them. The key is to use a threat intelligence platform (TIP) that filters out the noise and delivers the most relevant, actionable insights. Learn how to select a platform that fits seamlessly with your team’s expertise and existing infrastructure, enabling smarter, faster responses to potential threats.