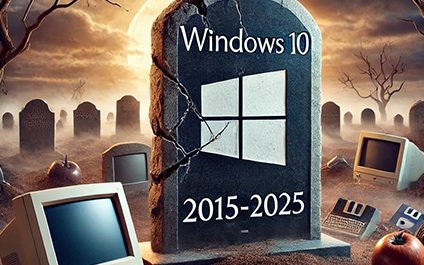
Important News: Microsoft will NO LONGER support Windows 10 after October 2025! While these PCs will still work after the official end date of October 14, 2025, Microsoft will no longer provide product key free services that keep your device working properly and securely.
Blog
Tech tips, news, and expert insights
Online privacy: Why private browsing matters
6 important battery-saving tips for iPhone users
The TikTok Chase Bank Glitch: A Lesson in Cybersecurity

Introduction
The recent TikTok trend, dubbed the “Chase Bank glitch,” serves as a stark reminder of the dangers of unverified financial advice on social media. While the claims of a glitch that allowed users to withdraw large sums of money without sufficient funds were initially met with excitement and disbelief, the reality was far more sinister.
How Microsoft Copilot Got Hijacked

Introduction
Have you heard about the recently patched vulnerability in Microsoft 365 Copilot, which exposed sensitive data through a novel AI-enabled technique called “ASCII Smuggling?”
This technique uses special Unicode characters that resemble ASCII text but are invisible to the user interface, allowing attackers to embed malicious code within seemingly harmless text.
Cyber Extortion Is NOT Just a Concern for Your Boss
Real Site or Typosquat? Here’s How to Tell

Introduction
What if you click on the link by mistake, or simply because you don’t stop to more carefully examine the email? Then, we run into another problem: Typosquatting.
This happens when scammers create lookalike websites so you believe that you are on the legitimate landing page of whatever organization the hacker is trying to emulate.
Encryption: The Invisible Shield Protecting Your Data
Outdated Technology Is Costing Your Organization Money

Is your organization currently bleeding money due to its reliance on outdated technology? The answer is likely yes. A recent survey by Deloitte revealed that a staggering 82% of companies failed to meet their cost-reduction targets last year, with an inefficient technology infrastructure being the primary culprit.