Introduction
What if threat actors could see everything that you did online? Everything you searched, every message you sent, every password you entered?
If your device is infected with the right software, then this nightmare can become all too real!
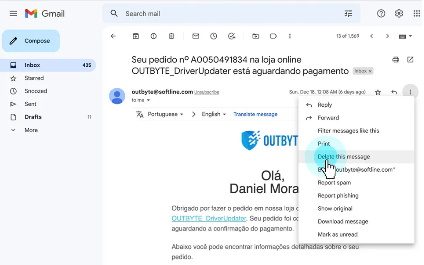
Keylogging technology records and stores the keystrokes entered on a computer.